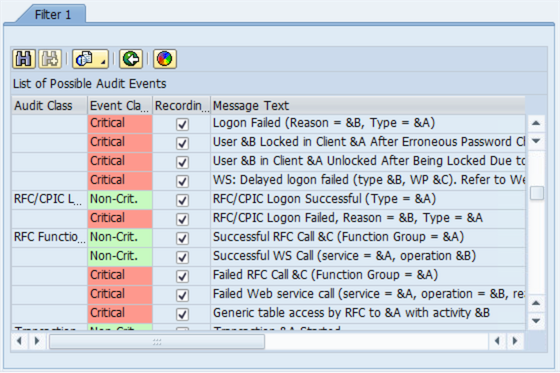
What is SAP Security Audit Log | SAP Security Audit Log analysis | SAP Security Audit Log Sizing and Disk Space | SAP security | Enterprise threat detection for SAP | ETD

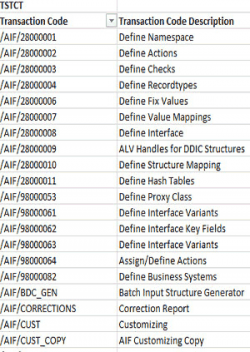
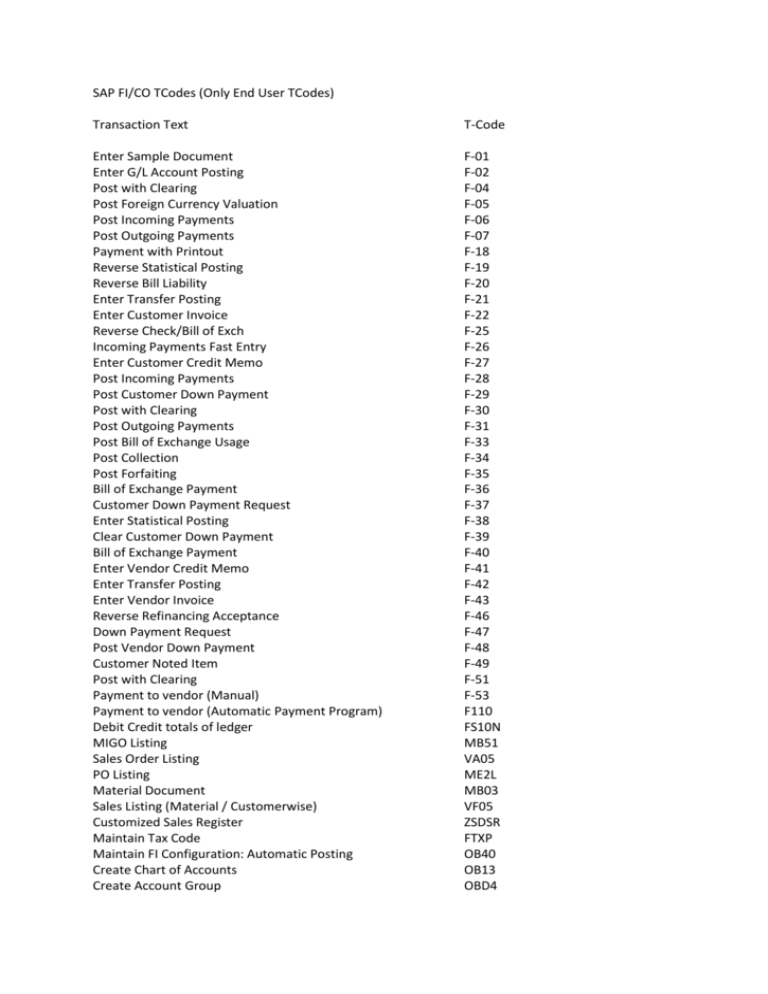
How to find which Transaction Codes was Deleted in SAP S/4 HANA compared to SAP ECC 6.0? | SAP Blogs

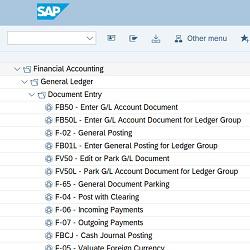
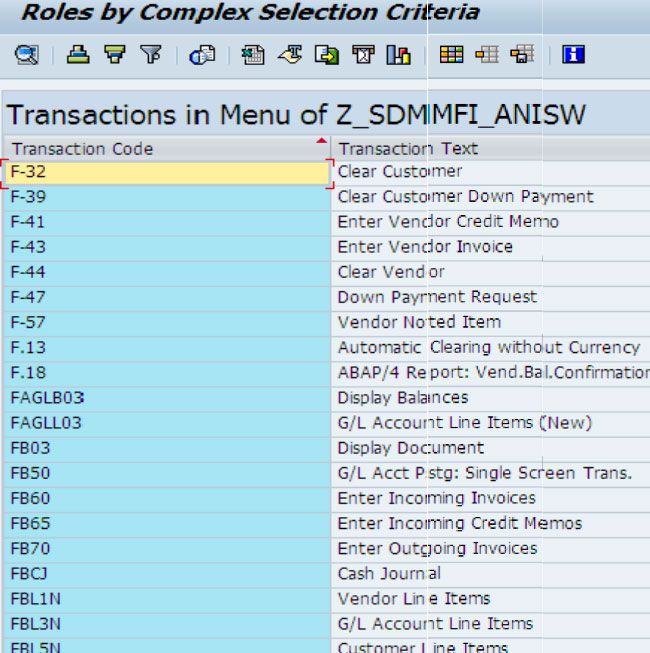
Identity Management and SAP Users, Roles and Transactions - Part1 - IBM Security Identity and Access









.jpg)