City of Northfield, Minnesota - Update: Pills Related to Recent Overdoses Contain Carfentanil The Northfield Police Department has received lab results from the Minnesota Bureau of Criminal Apprehension Forensic Science Lab regarding
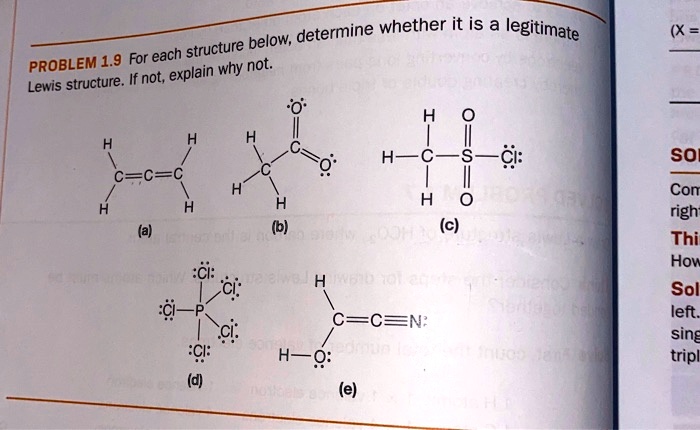
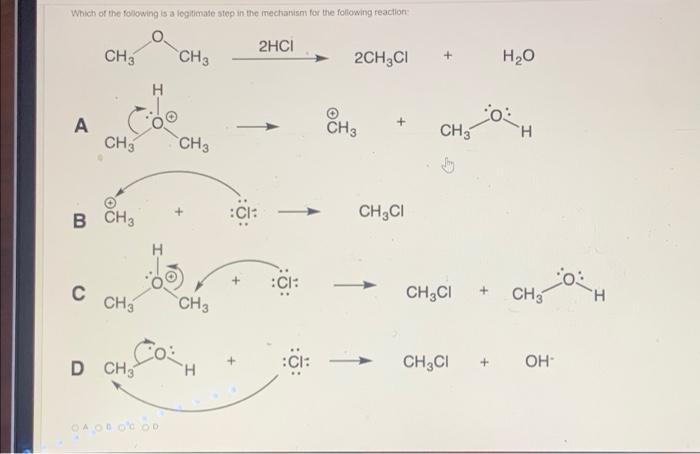
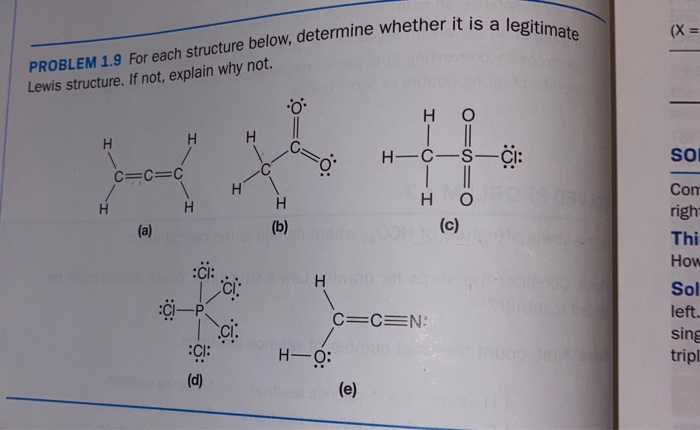
SOLVED: determine whether it is a legitimate structure below; PROBLEM 1.9 For each explain why not: Lewis structure. If not; H= Ci: SO Com righ Thi How Sol left sing tripl (c) '

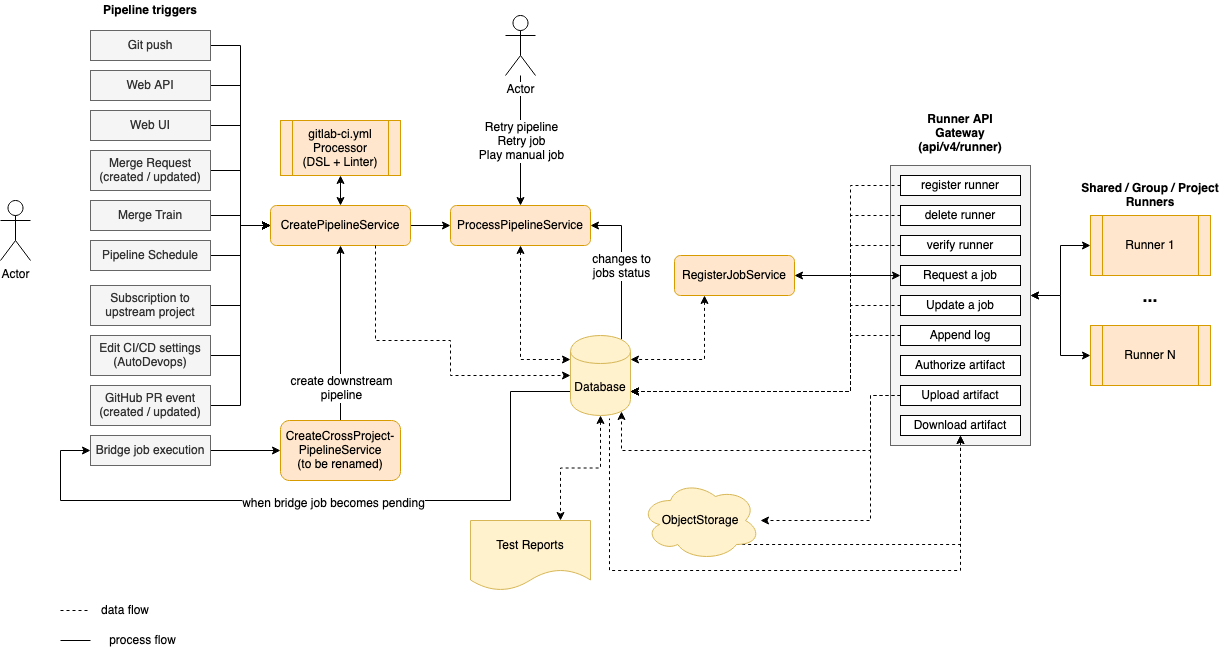
Operational phase: A legitimate node request initiation process with... | Download Scientific Diagram

04 June 2019, Venezuela, Caracas: A man is sitting in a camp where former oil workers are attracting attention with a hunger strike. Some men have been on hunger strike for six