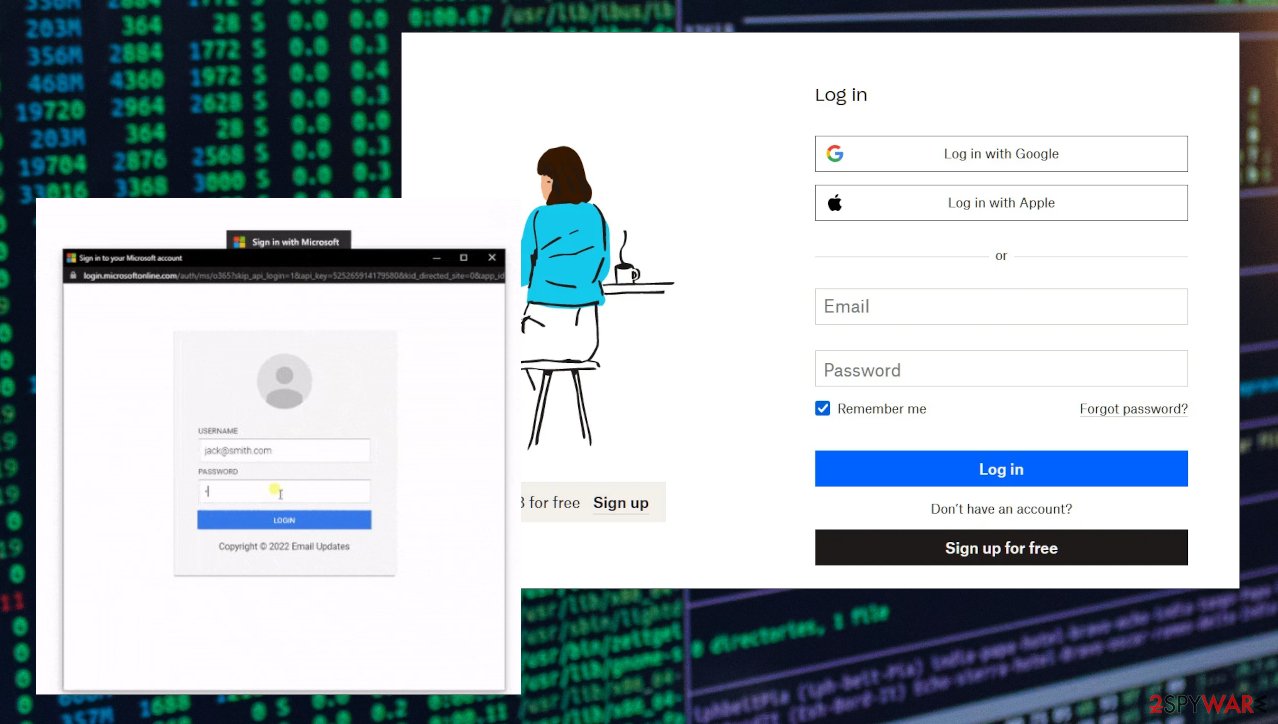
Illustration of a backdoor attack to generate a fake news headline on... | Download Scientific Diagram

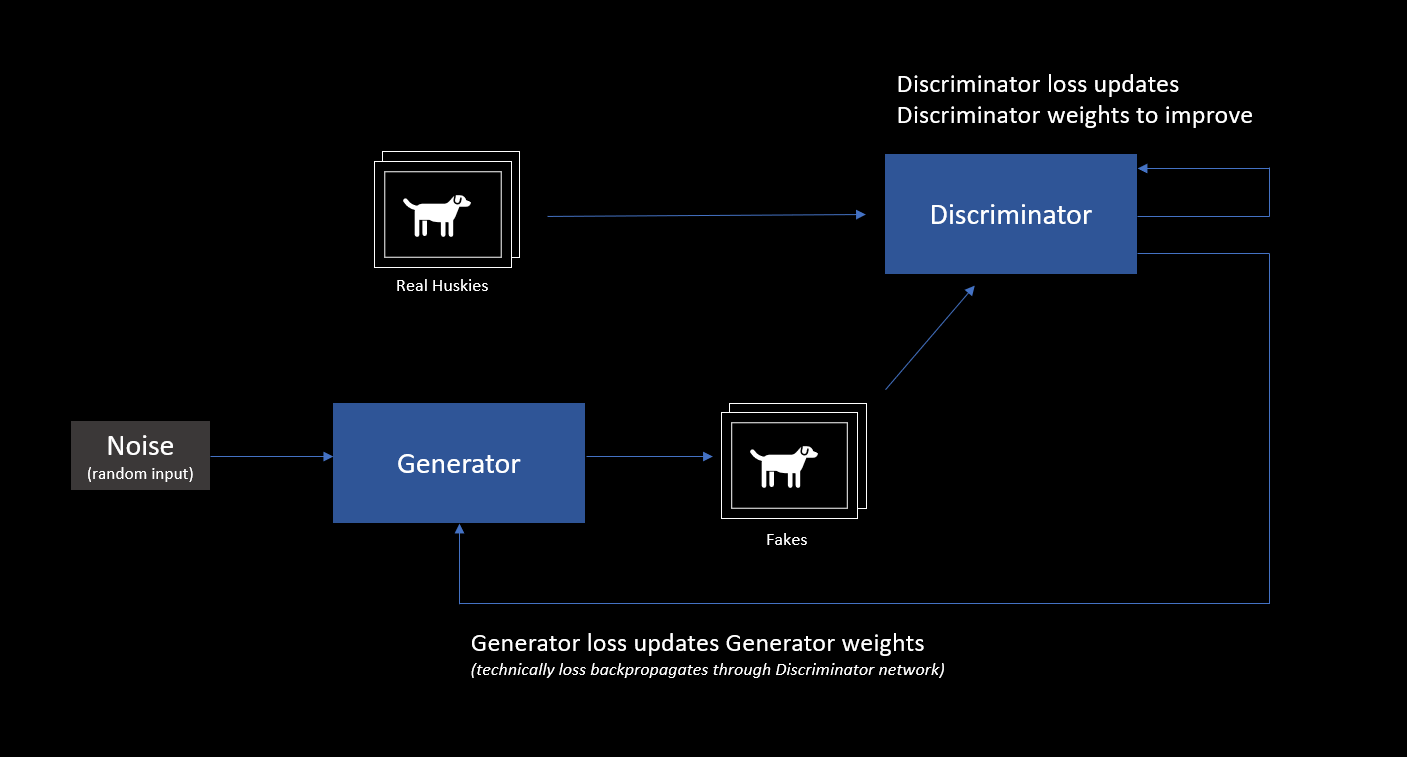
Applied Sciences | Free Full-Text | Palmprint False Acceptance Attack with a Generative Adversarial Network (GAN)
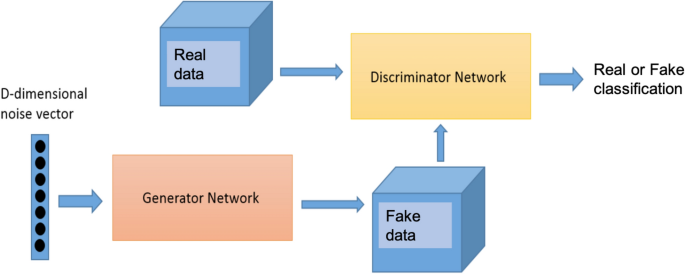
Synthetic flow-based cryptomining attack generation through Generative Adversarial Networks | Scientific Reports







![Spoilerless] Was playing with the fake spoiler generator when suddenly... : r/ShingekiNoKyojin Spoilerless] Was playing with the fake spoiler generator when suddenly... : r/ShingekiNoKyojin](https://external-preview.redd.it/ilJ6BJpikhbogQcKLUfKsuE9NgHbMLkKBJogVCG5MxM.png?auto=webp&s=b9435fb7f0bf5b960fc3faee1103460ca60309a0)