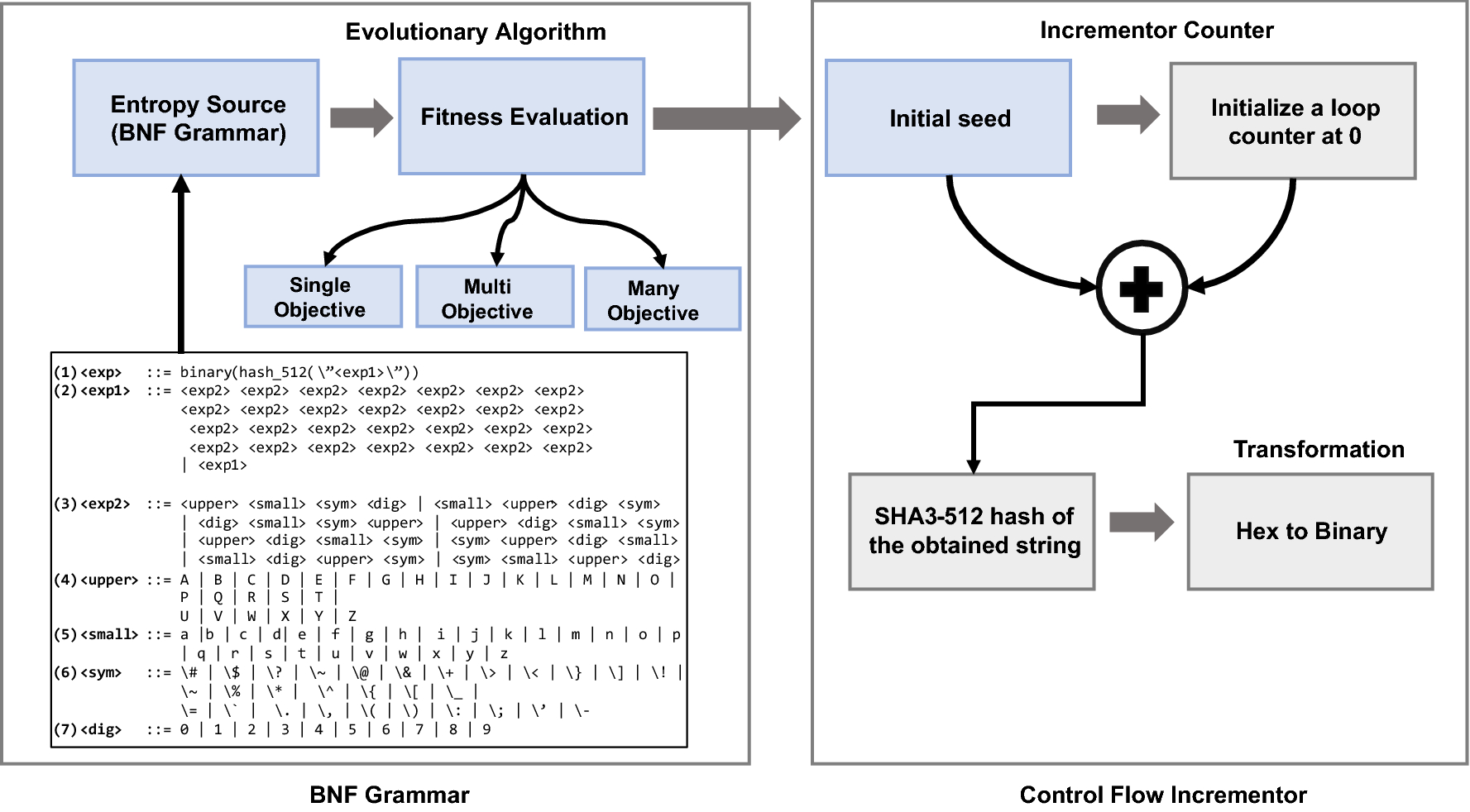
Design of a cryptographically secure pseudo random number generator with grammatical evolution | Scientific Reports

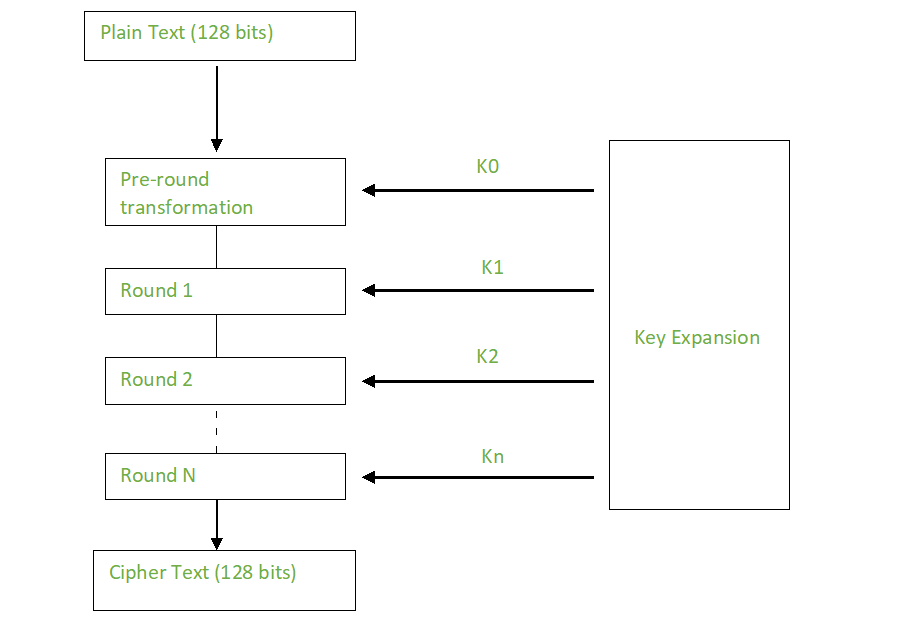
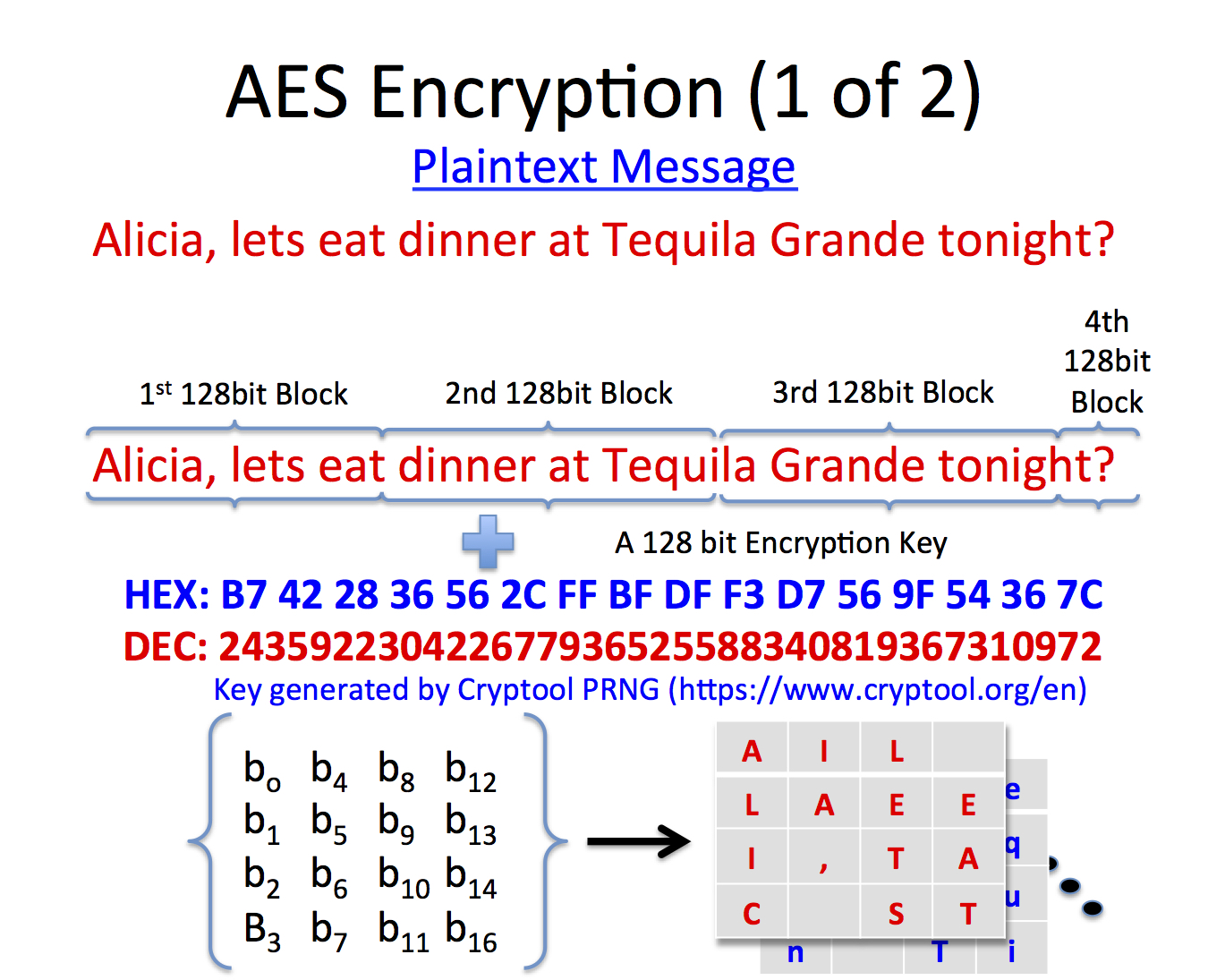
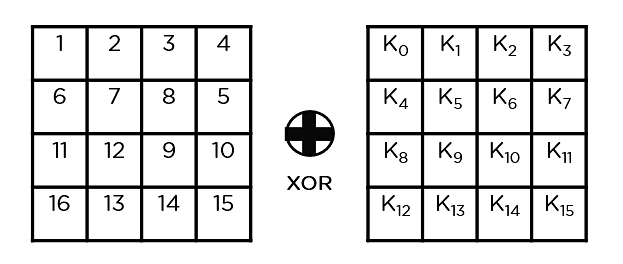
Hardware Software Co-Simulation of Obfuscated 128-Bit AES Algorithm for Image Processing Applications | Semantic Scholar

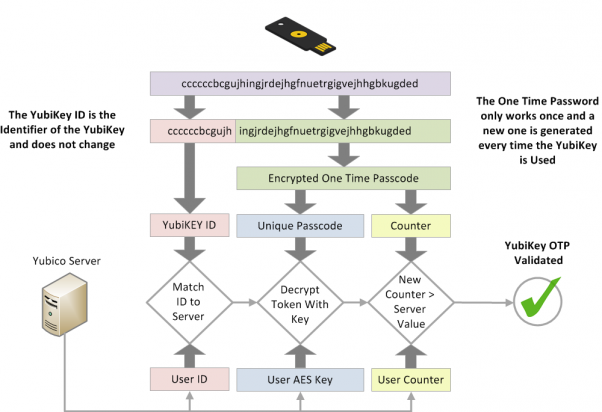
Security aspects of removing a user from an organization or collection - Vaultwarden Forum (formerly Bitwarden_RS)