Trojan Hidden in Fake Revolutionary Documents Targets Syrian Activists | Electronic Frontier Foundation
There are several fake folders on my pc. They're most likely viruses. I updated Norton and used full system scan. It says no viruses. What do I do? - Quora

Fake News Infomation Conceptfolder Register On A Dark Wooden Desk Stock Photo - Download Image Now - iStock

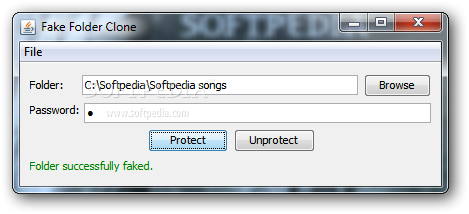
Gallery photo lock Highlights: 1. Fake Password for Vodlocker: Video hider / Hide my folder App has Secondary space to… | Hidden photos, Photo folder, Locker app

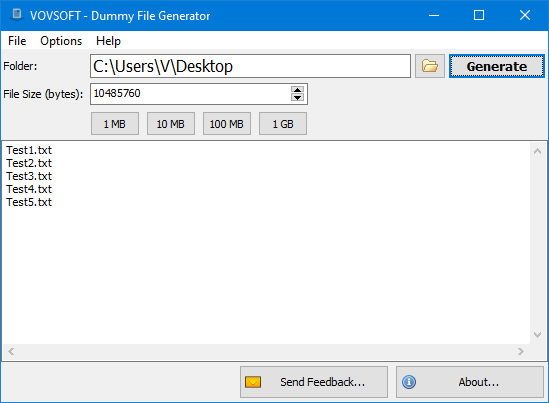
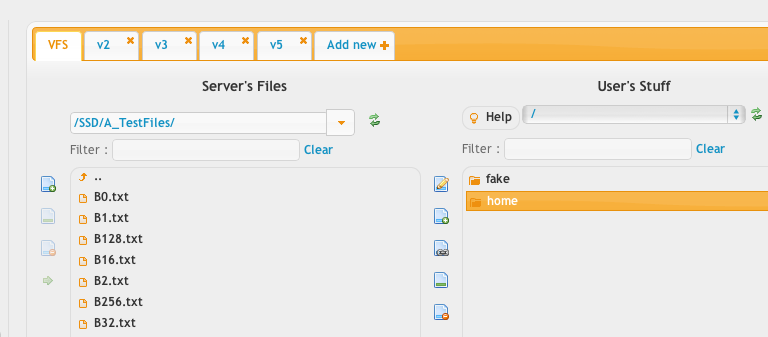
5 Ways to Create Fake Dummy File on USB Flash Drive to Enable Write Protect and Prevent Modification • Raymond.CC - Page 2