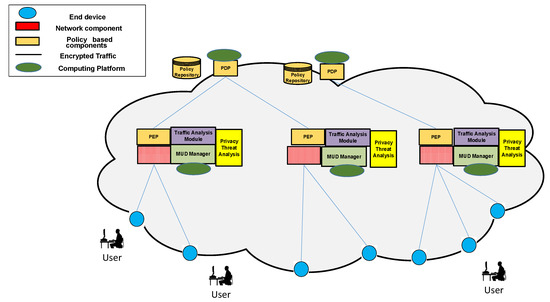
Symmetry | Free Full-Text | Mitigation of Privacy Threats due to Encrypted Traffic Analysis through a Policy-Based Framework and MUD Profiles

Information-Centric Networking solutions for the Internet of Things: A systematic mapping review - ScienceDirect
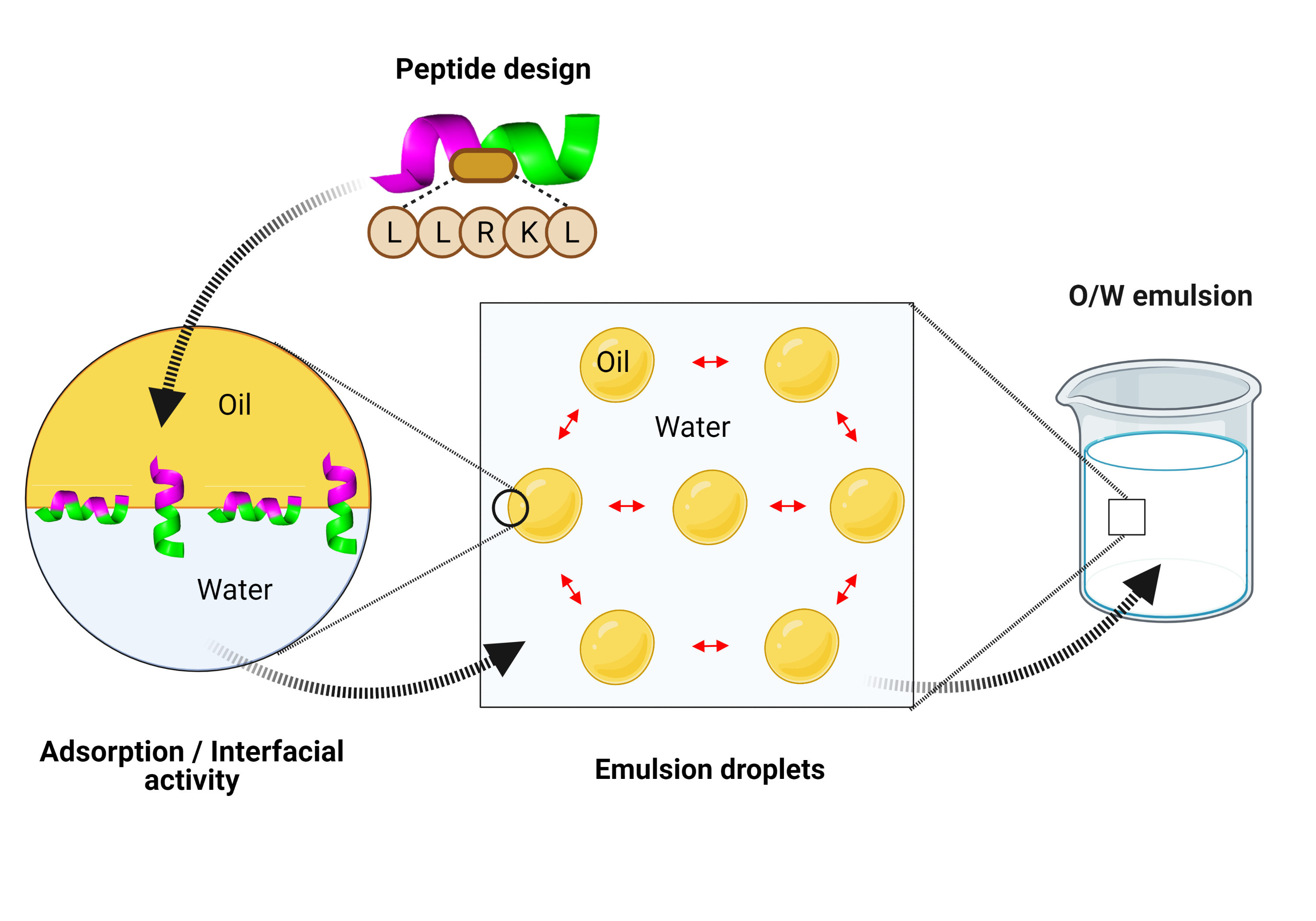
IJMS | Free Full-Text | Emerging Emulsifiers: Conceptual Basis for the Identification and Rational Design of Peptides with Surface Activity

Add new data source too small to see - THWACK Community Discussions - THWACK Command Center - THWACK
![Cisco ASA 5500 Series Configuration Guide using the CLI, 8.4 and 8.6 - Configuring the Content Security and Control Application on the CSC SSM [Cisco ASA 5500-X Series Firewalls] - Cisco Cisco ASA 5500 Series Configuration Guide using the CLI, 8.4 and 8.6 - Configuring the Content Security and Control Application on the CSC SSM [Cisco ASA 5500-X Series Firewalls] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/100001-200000/140001-150000/148001-149000/148387.ps/_jcr_content/renditions/148387.jpg)